Cybercrime Law Enforcement and E-Government Transitional Issues
Transcript of Cybercrime Law Enforcement and E-Government Transitional Issues
Table of Contents
Page #
I. Introduction3
II. The Federal Government: Cybersecurity Requirements, theLaw, RegulationsAnd the Private sector
4
IIa. The Politics of Cybersecurity5
IIb. Cybersecurity and Federal Laws and Requirements7
IIc. Federal Laws, Requirements, and Regulations at Work8
III. Effect of Federal Laws, Requirements, and Regulations on Private Industry 9
IIIa. The Impact of Failing to Comply with Federal Requirements, the Law, and Regulations
9IIIb. Private Industry’s Responsibility to Comply
10IIIc. Results from Lack of Compliance
11
IV. Conclusion 11
2
References12
I. Introduction
Cybercrime is a growth industry and the possibility of it growing
even faster is significant. The fact that technology moves faster
than the lawmakers adds fuel to the fire. Those who break the law
do not care how many laws are passed or how severe the punishment
so new and more stringent laws may have no impact on cybercrime.
The Federal government is also dealing with the lack of laws and
directives governing cybercrime. What about the private sector?
Industry must deal with not only Federal laws and guidelines but
state and international laws as well. These myriad of laws,
3
guidelines, and directives at times present obstacles to
initiative and entrepreneurship needed to help combat cybercrime.
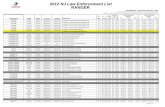
Cybercrime continues to grow at an alarming rate. The below graph
from the U.S. Department of Justice demonstrates the growth in
cybercrime from 2001 through 2012.
This paper will aim to bring to light some of the questions
facing the law making and law enforcing community
II. The Federal Government: Cybersecurity Requirements, the Law,RegulationsAnd the Private sector
The government of the United States is responsible for protecting
the infrastructure of certain defense critical industries. The
4
government also collaborates with the states to help secure the
electric grid, water supplies and yes the internet. The
electricity producing utilities operate using Supervisory Control
and Data Acquisition (SCADA) systems to monitor and program the
system. These systems are vulnerable to attack from
cybercriminals. The need to improve the security of these systems
has been a major concern for several years and a new paradigm for
how they are secured is needed (Patek, S. et.al, 2009). Having
said that, what is the Federal government doing to make our
critical infrastructure more secure?
GEN. Keith Alexander is the Commander of the U.S Cyber Command
and the Director of the National Security Agency. During a
conference hosted by Georgia Tech, the GEN implied that lawmakers
must create laws that allow the private sector and the public
sector to share information and technology freely (Corbin, 2013).
The GEN also stated that the Federal oversight of private
industry is a challenging problem. The problem is controllable by
the Federal security agencies becoming full-fledged partners with
the private sector. There are cooperative efforts underway now
that may help with the problem of how involved the government 5
should be. The National Institute of Standards and Technology is
a sponsoring government agency of the National Cybersecurity
Center of Excellence (CoE). The intent of the CoE is to foster
the cooperation between the public and private sector to resolve
the security issue regarding how much Federal involvement is
enough.
There are many government contracting companies around that
house, transport and store critical data to the nation’s
security. These organizations must meet all Federal requirements
on security both physical and cyber. It is not abuse to expect
these organizations to adhere to the strict policy and procedures
outlined by the government. Electricity suppliers are equally as
susceptible to Federal oversight. The nation’s power supply is
critical and should have some Federal involvement. The government
must play a role in securing the nation even if that security
impeaches the private sector.
IIa. The Politics of Cybersecurity
Two very different frames of thought polarize the United States
now. There are those that feel that the government must be
6
involved in every aspect of our lives from providing day-care for
children to providing food and shelter to providing medical care
for all citizens. On the opposite side there are those who
believe that the less government is involved with its citizens
the better.
The Constitution guarantees the pursuit of happiness, it does not
guarantee happiness, nor does it guarantee medical care,
education, or even food. It also does not guarantee a totally
secure computer network to control the electric power distributed
to the country. It is difficult to state where the line of
demarcation is for Federal involvement but it is a logical
expectation to safeguard national secrets and ensure as secure an
environment as possible. The constitution does state that the
government should provide for the common defense and it is
arguable that cybersecurity is a part of the common defense.
There are those that support the use of counter attack to try to
deter cybercrime. The Department of Homeland Security reports in
the Homeland Security News Wire that the DHS is developing a
system that would allow offensive actions against the attackers
of networks that support National security data and or control 7
SCADA systems. Those who oppose the insertion of the government
into our lives will certainly have strong feelings about the
possibility of damaging the system of a child hacker just having
some fun.
The financial sector of the U.S. economy is large and effects
many people around the world. In 2012, the Ponemon Institute
estimated that over 60% of cybercrime committed in the United
Sates was financial fraud.
The Patriot Act also provides an anti-money laundering section to
attempt to cut off financing for terrorist acts. The Act made
strict record keeping by financial institutions mandatory and the
8
use of off shore banks closely scrutinized. The estimate is that
this alone stopped several terrorist acts after the freezing of
financial accounts. The Act did not seem to discourage financial
fraud in the global economy as the Ponemon chart shows.
IIb. Cybersecurity and Federal Laws and Requirements
Where does the authority for the Federal government to regulate
cybercrime come from? Article 1 section 8 of the U.S.
Constitution authorizes congress to regulate commerce with
foreign nations, and among the various states. Most power
generated and distributed in the US is produced in a different
state than sold. This would mean that in most instances the power
sold passes across state lines, this would give the Federal
government, specifically the legislative branch, power to
regulate these transactions. Add to that the fact that these
systems controls are SCADA systems then common defense from the
Constitution argument also comes into play.
9
After the tragic events of September 11, 2001, many laws came
into being. One of them is the Patriot Act. Section 105 of the
Patriot Act instructed the Director of the Secret Service to
establish a National network called the Electronic Crime Task
Force. The task force members established offices in metropolitan
areas with the sole purpose of preventing, detecting, and
investigating electronic crimes. Cybercrime falls under the
jurisdiction of the task force. The task force has grown from
seven offices to 24.
The Computer Fraud and Abuse Act of 1986 established that it is a
crime to access a computer or network without proper
authorization (Adams, 1996). The same legislation covers crimes
such as theft of data, damage to computers or networks, and
identity theft. The penalties for such actions are severe and can
lead to a lengthy prison term. However, the amount of cybercrime
has increased since the passing of the Act.
The National Institute of Standards and Technology (NIST) work
with members of industry and academia to develop standards for
computing and networking. One of the latest publications is
10
Special Publication 800-145 (Draft) The NIST Definition of Cloud
Computing provides security guidelines that should be used when
establishing a cloud based environment. The guidelines help
federal contractors establish networks that adhere to the strict
security policy in the publication.
IIc. Federal Laws, Requirements, and Regulations at Work
The Patriot Act provided wide sweeping reforms regarding how the
various intelligence agencies and law enforcement agencies share
information. As an example, prior to the Patriot Act it was not
permissible for the FBI to share information from a suspected
terrorism crime with the CIA or NSA. The ability to share this
information can help the intelligence community track possible
terrorists and cybercriminals as well.
There are those that claim that the Patriot Act is much too
invasive to the privacy of the citizens. The Act provides for the
wiretapping and eaves dropping of the conversations of ordinary
people (Hayden, 2013). Those who are complaining should read the
Constitution. The Forth Amendment allows for the set aside of
11
certain civil liberties if not unreasonable and there is probable
cause for the good of the Nation.
In May of 2009, President Obama established the Comprehensive
National Cybersecurity Initiative based on the recommendations
made by the Cyberspace Policy Review group. One of the purposes
behind the initiative is to encourage the Federal government to
work with state and local government and the private sector to
become a more capable defense force against the cyber threats
facing the country. The NIST National Cybersecurity Center of
Excellence is an example of how all stakeholders can come
together to work toward the common good.
III. Effect of Federal Laws, Requirements, and Regulations on
Private Industry
The rules that industry must follow due to Federal regulation and
law can be burdensome on the companies they affect. Often there
is a need for expenditures for new equipment, policy, or
12
procedures. It is not unreasonable to expect a private sector
business doing business with the Defense Department to comply
with national security requirements when working with National
defense data. Recently top-secret information regarding some of
the nation’s most advanced weapons was stolen by cybercriminals
(Nakashima, 2013). The report in the Washington Post stated that
several of the major weapon systems such as the Patriot Anti-
Aircraft system, the Navy’s new fighting ship, and the F-35 Joint
Strike Fighter. The companies that reported their networks had
been breached included Northrop Grumman, Lockheed Martin, Boeing,
and Raytheon. Last year legislation to enforce more stringent
network and cyber security measures stalled. Once again, it seems
like our worse enemy is ourselves.
IIIa. The Impact of Failing to Comply with Federal Requirements, the Law,
and Regulations
As discussed in the previous section, the need for the private
sector to adhere to the stringent security measures outlined by
the Department of Defense is critical to our national security.
The fact that the companies mentioned were penetrated and data
13
extracted is not surprising because they were most likely in
compliance with all security requirements that government
contractors must follow. The question then is, are those security
requirements sufficient to secure the nations secrets? The DoD
has specific requirements for each piece of equipment networked.
These requirements called Security Technical Implementation
Guides (STIGs) outline the minimum-security requirements for that
equipment. The DoD also has publication that describe security
process and procedures that must be followed for the network and
anything connected to the network such as Blackberries,
smartphones, and tablets. Failure for any entity, Federal of
private, may lead to denial of access to the network. The
security measurers mentioned are used by all of the companies
that were compromised leading to stealing of critical weapons
system data.
There seems to be a legitimate argument that compliance with the
minimum requirements is not sufficient. It is arguable that the
security products, process, and procedures cannot keep up with
the pace of those who develop methods for penetrating networks
and extracting valuable data from them. The computer anti-virus 14
provider McAfee reports nearly 100,000 new malware signatures
each day. These numbers look staggering, and they are. It may be
an impossible task to go beyond the minimal requirements when in
fact the requirements should probably change every day.
IIIb. Private Industry’s Responsibility to Comply
Private companies that work with the Federal government on
projects of national security must comply with all security
standards recommended by the government. That is not to say that
they should not go beyond the minimum requirements if they have
the resources and knowledge to do so. Companies that provide the
operation of critical infrastructure such as water, electricity,
freight movement, and the internet must conform to the latest and
best security posture as possible. The government working hand-
in-hand with the private sector should be able to come to a
rational approach to an overarching security posture to secure
critical systems. The companies that use SCADA systems to control
our electric grid and those government contractors supporting our
national defense have both a moral and a legal obligation to make
the country as secure as possible.
15
IIIc. Results from Lack of Compliance
In September of 2012 the company, Telvent reported that its
networks were penetrated (Perlroth, et.al, 2013). This may not
seem like a very important issue until discovered that Telvent is
the company that monitors a great portion of the nation’s oil and
gas pipelines. It is feasible to think that if a cybercriminal is
able to hack into the control network that they can then disrupt
the flow of gas and oil. The SCADA systems controlling the
pipelines are susceptible to many types of attacks and the
Telvent has a great responsibility to secure those systems and
protect the flow of oil in our country.
The companies who had the technical plans for our advanced
weapons systems must also do a better job in protecting the
information entrusted in them for our national security.
Following the minimal standards for security must no longer be
the paradigm; instead, the paradigm should be what are the best
security practices, equipment, and procedures available at the
16
current point in time. This would mean that the security posture
of the company should change as the threat model changes.
IV. Conclusion
The U.S. will desperately try to keep up with the constantly
changing cyber landscape by attempting to pass laws and organize
working groups. The criminals will continue to move faster and in
the instances of an enemy nation state have seemingly unending
resources to attack our networks. This dance will continue, as
the bad people seem to have an upper hand.
It may be a wiser choice not to emphasize passing laws the
criminals will no obey anyway. More time and resources into
research and development of security measures for networks and
networked devices may provide results that are more meaningful.
References
Adams, J. A. M. (1996). Controlling cyberspace: applying the computer fraud and abuse act to the internet. Santa Clara Computer & High Tech. LJ, 12, 403.
U.S. to help protect private companies from malicious cyberattacks. (2013, May 21). Homeland Security News Wire, Retrieved from http://www.homelandsecuritynewswire.com/dr20130524-report-u-s-companies-should-consider-counterhacking-chinese-hackers
17
Corbin, K. (2013). National Security Agency: 'We Need to See What's Going on'. Cio (13284045), 14.
Doyle, C. (2012). Cybersecurity: Cyber Crime Protection Security Act (S. 2111): a Legal Analysis. Congressional Research Service, Library of Congress
Etzioni, A. (2011). N334 Private Sector Neglects Cyber Security
Fidler, D.P. (2012). Recent Developments and Revelations Concerning Cybersecurity and Cyberspace: Implications for International Law. American Society of International Law
Harper, J. (2012). Cybersecurity: Will Federal Regulation Help?.
Hayden, M. (2013). The Patriot Act. BYU Prelaw Review, 27, 117-127.
Nakashima, E. (2013, May 27). Confidential report lists u.s. weapons systems designs compromised by Chinese cyberspies. The Washingtom Post. Retrieved from http://www.washingtonpost.com/world/national-security/confidential-report-lists-us-weapons-system-designs-compromised-by-chinese-cyberspies/2013/05/27/a42c3e1c-c2dd-11e2-8c3b-0b5e9247e8ca_story.html
PATEL, S. C., BHATT, G. D., & GRAHAM, J. H. (2009). Improving TheCyber Security of Scada Communication Networks. Communications Of The ACM, 52(7), 139-142.
Perlroth, N., Sanger, D., & Schmidt, M. (2013, March 3). As hacking against U.S. rises, experts try to pin down the motive. The New York Times. Retrieved from http://www.nytimes.com/2013/03/04/us/us-weighs-risks-and-motives-of-hacking-by-china-or-iran.html?pagewanted=all
Rhodes, K. A., & Willemssen, J. (2004). Technology Assessment: Cybersecurity for Critical Infrastructure Protection: GAO-04-321.GAO Reports, 1.
Slade, R. (2006). Digital courts, the law and evidence. In H. Bidgoli (Ed.), Handbook of Information Security, (pp. 459-466). Hoboken, NJ: John Wiley & Sons.
18